-
Blog
Benefits of Hosted IP PBX for Your Business Communication
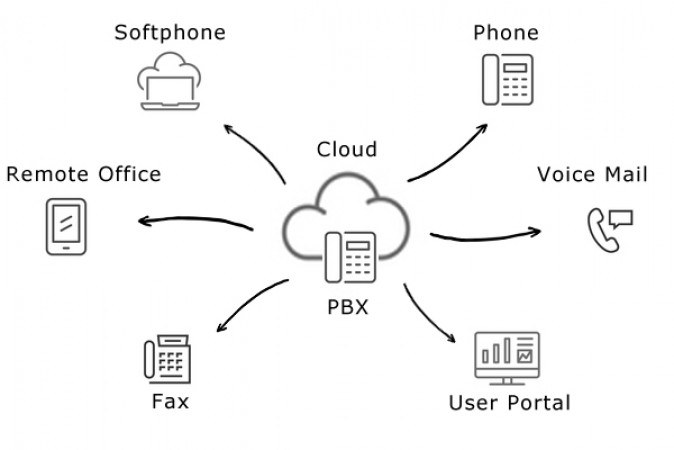
In today's digital age, effective communication is crucial for businesses to thrive. Traditional phone systems have been replaced by innovative solutions that offer more flexibility, scalability, and cost-effectiveness. One such solution is a hosted IP PBX (Private Branch Exchange), which leverages the power of the internet to provide feature-rich communication services. In this blog post, we will explore the advantages of hosted IP PBX and why it could be the perfect fit for your business communication needs. ...
Read MoreWhat is IP PBX?

An IP PBX, or Internet Protocol Private Branch Exchange, is a business phone system that uses Internet Protocol (IP) to transmit voice and data. IP PBX systems are becoming increasingly popular as businesses look for ways to save money on their telecommunications costs and improve their communication capabilities. ...
Read More3-2-1Backup Rule
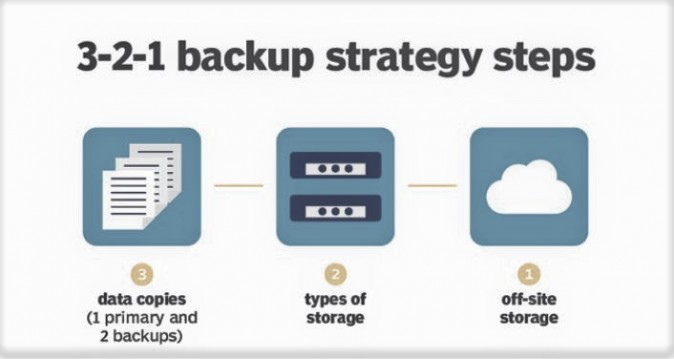
What does 3-2-1 backup mean, and what is the best way to achieve it? Keep reading for a 3-2-1 backup rule overview ...
Read MoreWhat is Desktop as a Service (DaaS)?

Desktops-as-a-Service or simply DaaS, securely delivers virtual apps and desktops from the cloud to any device or location. Desktops-as-a-Service or simply DaaS, is the delivery of a fully managed virtual desktop instance (VDI), hosted on cloud infrastructure. DaaS enables users to access corporate applications and data via a familiar Microsoft Windows desktop experience on almost any device connected to the internet. ...
Read MoreWhat does secure web connection actually do?

Web browser, these days has become more and more of an everyday tool, we are increasingly uploading accessing and information about ourselves, our finances, and company data through it. ...
Read More3 Reasons Why You Should Consider Using Professional IT Consulting

IT consulting is a cost-effective strategy for organizations that rely on IT performance to support their business operations. A managed IT services provider with IT consulting service can add immediate value to an organization by providing access to the advanced tools and technology expertise your company doesn’t have. ...
Read More